Adware
Содержание:
- An ounce of prevention vs. a pound of cure
- How do I prevent Trojans?
- How do I get adware?
- Who does Emotet target?
- All about adware
- How can I tell if I have a malware infection?
- Как Malware получает котроль над системой
- How do I get malware?
- Mac spyware
- Как самому проверить компьютер на зараженность Malware
- How do I get spyware?
- How does malware affect my business?
- What’s the difference between antivirus and anti-malware?
- The future of cybersecurity programs (which is already here)
- Do Macs get malware?
- What is malware?
- How Malwarebytes Premium protects you
- How can I tell if my iPhone or iPad has malware?
- How can I remove Emotet?
- Who do spyware authors target?
An ounce of prevention vs. a pound of cure
From desktops and laptops to tablets and smartphones, all our devices are vulnerable to malware. Given a choice, who wouldn’t want to prevent an infection instead of dealing with the aftermath?
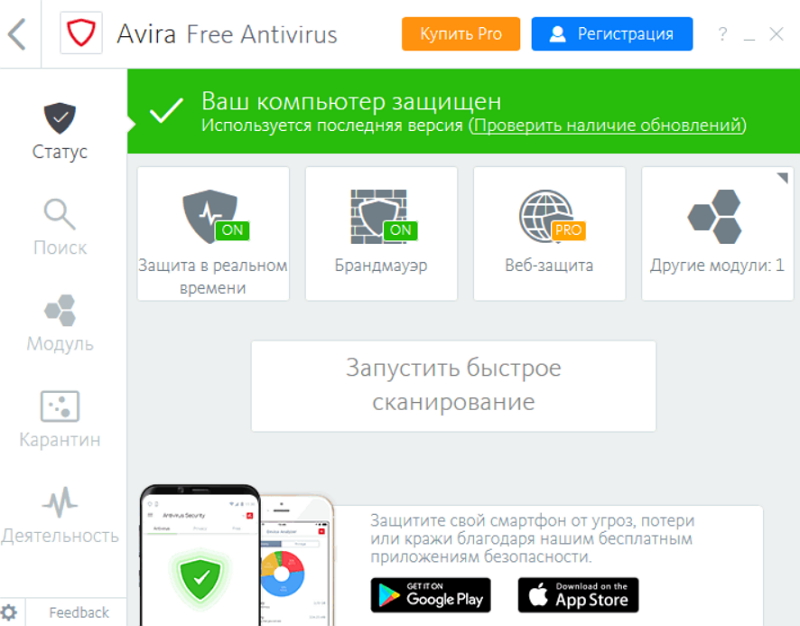
Traditional antivirus alone is not up to the task, as evidenced by the regular stream of newspaper headlines reporting yet another successful cyberattack.
So what should you do to stay safe? What kind of cybersecurity software—antivirus or anti-malware—should one choose to address a threat landscape that consists of legacy viruses and emerging malware?
The fact is, traditional antivirus alone is not up to the task, as evidenced by the regular stream of newspaper headlines reporting yet another successful cyberattack. It is inadequate against emerging zero-day threats, allows ransomware to successfully hijack computers, and doesn’t completely remove malware. What’s needed is an advanced cybersecurity program that is flexible and smart enough to anticipate today’s increasingly sophisticated threats.
Malwarebytes for Windows fulfills this need for advanced cybersecurity (along with Malwarebytes for Mac, Malwarebytes for Android, and Malwarebytes business solutions). Malwarebytes products protect against malware, hacks, viruses, ransomware, and other ever-evolving threats to help support a safe online experience. Our AI-enhanced, heuristics-based technology blocks threats that traditional antivirus isn’t smart enough to stop.
For an additional layer of protection, consider Malwarebytes Browser Guard. It’s the browser extension that stops annoying ads and trackers. Plus, it’s the world’s first browser extension that blocks tech support scams.
Industry watchers have cited Malwarebytes for Windows for its role in a layered protection approach, providing reliable protection without degrading system performance. It removes all traces of malware, blocks the latest threats, and performs scans fast.
Regardless of the cybersecurity you choose, your first line of defense is education. Stay up to date on the latest threats and protection by making the Malwarebytes Labs blog a regular read.
How do I prevent Trojans?
Since Trojans rely on fooling users into letting them into the computer, most infections are avoidable by remaining vigilant and observing good security habits. Practice a healthy skepticism about websites offering free movies or gambling, opting instead to download free programs directly from the producer’s site rather than from unauthorized mirror servers.
Another precaution to consider: change the default Windows settings so that the real extensions of applications are always visible. This avoids getting tricked by an innocent looking icon.
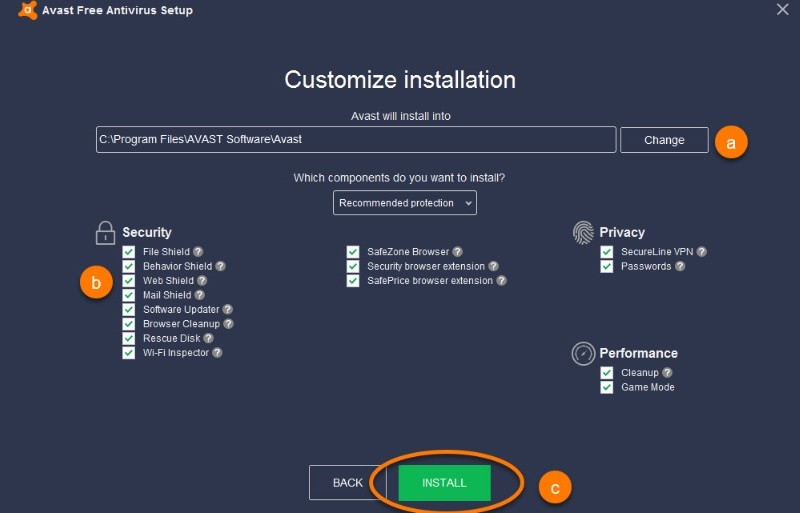
Other good practices besides installing Malwarebytes for Windows, Malwarebytes for Android, and Malwarebytes for Mac include:
- Running periodic diagnostic scans
- Setting up automatic updates of your operating system software, ensuring you have the latest security updates
- Keeping your applications updated, ensuring any security vulnerabilities are patched
- Avoiding unsafe or suspicious websites
- Being skeptical of unverified attachments and links in unfamiliar emails
- Using complex passwords
- Staying behind a firewall
How do I get adware?
There are two main ways by which adware sneaks onto your system. In the first one, you download a program—usually freeware or shareware—and it quietly installs adware without your knowledge, or permission. That’s because the program’s author signed up with the adware vendor. Why? Because the revenue generated by the advertisements enables the program to be offered gratis (although even paid software from an untrustworthy source can deliver an adware payload). Then the adware launches its mischief, and the user learns there’s a price to pay for “free.”
“There are two main ways by which adware sneaks onto your system.”
The second method is just as insidious. You’re visiting a website. Maybe it’s a trusted site; maybe
it’s a sketchy one. Either way, it can be infected with adware, which takes advantage of a vulnerability in
the user’s web browser to deliver a
drive-by download. After it burrows in, the adware starts collecting your information, redirecting you to
malicious websites, and throwing more advertisements into your browser.
Who does Emotet target?
Everyone is a target for Emotet. To date, Emotet has hit individuals, companies, and government entities across the United States and Europe, stealing banking logins, financial data, and even Bitcoin wallets.
One noteworthy Emotet attack on the City of Allentown, PA, required direct help from Microsoft’s incident response team to clean up and reportedly cost the city upwards of $1M to fix.
Now that Emotet is being used to download and deliver other banking Trojans, the list of targets is potentially even broader. Early versions of Emotet were used to attack banking customers in Germany. Later versions of Emotet targeted organizations in Canada, the United Kingdom, and the United States.
“One noteworthy Emotet attack on the City of Allentown, PA required direct help from Microsoft’s incident response team to clean up and reportedly cost the city upwards of $1M to fix.”
All about adware
Here’s how it happens. You go online with your nice, well-behaved browser, only to see it fly into a virtual
tantrum, as an onslaught of advertisements either pops up, slides in from the side, or otherwise inserts itself to
interrupt and even redirect your intended activity. And no matter how much you click to close those windows, they
keep buzzing you like flies at a picnic.
That bothersome phenomenon results from adware, short for advertising supported software. And just as your picnic
food attracts the pests that come after it, money—or the revenue generated by unbidden ads—is what draws adware to
your PC or mobile device. Below, we offer a short primer on adware, what it is, how you get it, what it tries to do
to you, how to deal with it, and what to do in the future to avoid this irritant.
How can I tell if I have a malware infection?
Malware can reveal itself with many different aberrant behaviors. Here are a few telltale signs that you have malware on your system:
- Your computer slows down. One of malware’s main effects is to reduce the speed of your operating system,
whether you’re navigating the Internet or just using your local applications. - A tidal wave of annoying ads that shouldn’t be there washes over your screen. Unexpected pop-up ads are a
typical sign of a malware infection. They’re especially associated with a form of malware known as adware. What’s more, pop-ups usually come packaged with other hidden malware threats.
So if you see something akin to “CONGRATULATIONS, YOU’VE WON A FREE PSYCHIC READING!” in a
pop-up, don’t click on it. Whatever free prize the ad promises, it will cost you plenty. - Your system repeatedly crashes, freezes, or displays a BSOD (Blue Screen of Death), which can occur on Windows
systems after encountering a fatal error. - You notice a mysterious loss of disk space, probably due to a bloated malware squatter which hides in your hard
drive. - There’s a weird increase in your system’s Internet activity.
- Usage of your system resources is abnormally high and your computer’s fan starts whirling away at full
speed—signs of malware activity taking up system resources in the background. - Your browser’s homepage changes without your permission. Similarly, links you click send you to an unwanted
web destination. This usually means you clicked on that “congratulations” pop-up, which downloaded some
unwanted
software. Likewise, your browser might slow to a crawl. - New toolbars, extensions, or plugins unexpectedly populate your browser.
- Your antivirus product stops working and you cannot update it, leaving you unprotected against the sneaky malware
that disabled it. - Then there’s the painfully obvious, intentionally non-stealthy malware attack. This famously happens with
ransomware, which announces itself, tells
you it has your data, and demands a ransom to return your files. - Even if everything seems to be working just fine on your system, don’t get complacent, because no news
isn’t necessarily good news. Powerful malware can hide deep in your computer, going about its dirty business
without raising any red flags as it snags your passwords, steals sensitive files, or uses your PC to spread to
other computers.
Как Malware получает котроль над системой
Для работы Malware требуется, чтобы пользователь его запустил, и это – только первый шаг. Достаточно часто Malware использует другие методы, чтобы предоставить себе наиболее вероятную гарантию хотя бы на единоразовый запуск в каждой из сессий работы системы
Для Malware исключительно важно производить запуск себя и резидентно присутствовать в памяти. И удобнее всего Malware прописываться при загрузке компьютера, а также при инициализации и переконфигурации системы
Основные места обитания Malware – файлы command.com, autoexec.bat и config.sys, файлы конфигурации в системах DOS и Windows при загрузке по стандартной схеме. Кроме того, часто Malware прячется в файлах главных шаблонов офисных приложений Word и Excel – Normal.dot и XLStart.
How do I get malware?
“Malware attacks would not work without the most important ingredient: you.”
Bottom line, it’s best to stick to trusted sources for mobile apps, only installing reputable third-party
apps, and always downloading those apps directly from the vendor—and never from any other site. All in all, there is
a world of
bad actors out there, throwing tainted bait at you with an offer for an Internet accelerator, new download
manager, hard disk drive cleaner, or an alternative web search service.
Even if you install something from a credible source, if you don’t pay attention to the permission request to install other bundled software at the same time, you could be installing software you don’t want. This extra software, also known as a potentially unwanted program (PUP), is often presented as a necessary component, but it often isn’t.
Another wrinkle is a bit of social
engineering that a Malwarebytes expert observed in the UK. The scam hit mobile users by taking advantage of a
common mobile direct-to-bill
payment option. Users visited mobile sites, unwittingly tripping invisible buttons that charge them via their
mobile numbers, directly billing the victims’ networks, which pass the cost onto their bill.
To be fair, we should also include a blameless malware infection scenario. Because it’s even possible that
just visiting a malicious website and viewing an infected page and/or banner ad will result in a drive-by malware download.
On the other hand, if you’re not running an adequate security program, the malware infection and its aftermath
are still on you.
Mac spyware
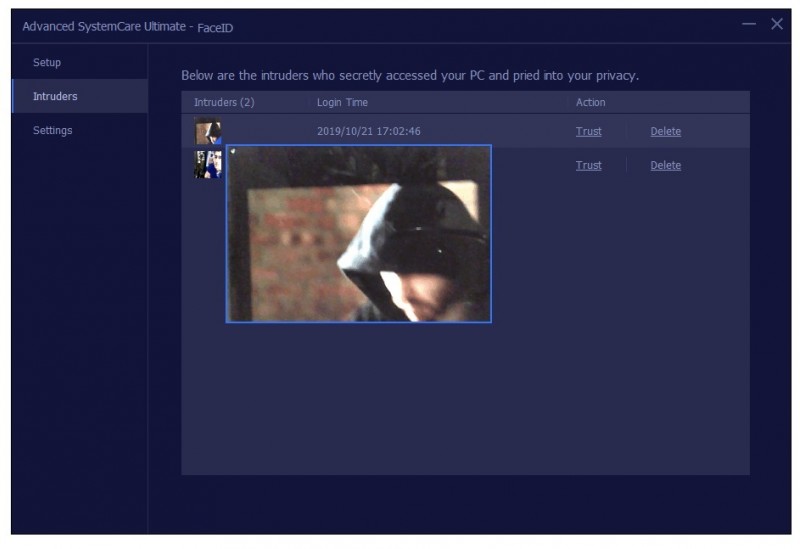
Spyware authors have historically concentrated on the Windows platform because of its large user base when compared to the Mac. However, the industry has seen a big jump in Mac malware since 2017, the majority of which is spyware. Although spyware authored for the Mac has similar behaviors as the Windows variety, most of the Mac spyware attacks are either password stealers or general-purpose backdoors. In the latter category, the spyware’s malicious intent includes remote code execution, keylogging, screen captures, arbitrary file uploads and downloads, password phishing, and so on.
“The industry has seen a big jump in Mac malware in 2017, the majority of which is spyware.”
In addition to malicious spyware, there’s also so-called “legitimate” spyware for Macs. This software is actually sold by a real company, from a real website, usually with the stated goal of monitoring children or employees. Of course, such software is a two-edged sword, as it’s very often misused, providing the average user with a way of accessing spyware capabilities without needing any special knowledge.
Как самому проверить компьютер на зараженность Malware
Резидентные программы — это такие процессы, которые работают и остаются в памяти после их исполнения. Такая форма дает возможность программе Malware иметь постоянный доступ к данным и, не спуская глаз, следить за всеми происходящими в системе событиями.
Помогут обнаружить резидентного Malware в памяти обычные системные утилиты, такие, как менеджер задач – Task Manager, вызываемый комбинацией клавиш Ctrl+Alt+Del. После ее вызова появится диалоговое окно, где в виде списка отобразятся все работающие на текущий момент задачи. Нужно проверить этот перечень на предмет наличия в нем резидентного процесса с присоединенным Malware.
Риск самостоятельного выполнения такой манипуляции по незнанию довольно высокий
Закрытие важной резидентной программы, которая критично влияет на системную работу, может вызвать даже «синий экран смерти» или запустить перезагрузку. Ответить однозначно на вопрос о том, действительно ли конкретная резидентная программа не относится к работе системы, даже не всем профессионалам и гикам под силу
Можно поковыряться в руководстве по ОС, или поискать незнакомую программу из списка менеджера задач в интернете. Если по результатам поисковых мероприятий вы не нашли ничего существенного, или каких-либо указаний на то, что перед вами зловредный Malware, лучше не трогайте этот процесс.
Malware очень часто берет себе имена процессов, которые чрезвычайно похожи на имена стандартных процессов. В данном случае глядя на него, вы можете подумать, что это нормальный процесс, однако это будет не так. К примеру, вместо процесса WSOCK23.dll, который отвечает за обработку функций сокетов, можно увидеть поддельный процесс WSOCK33.dll. Другие варианты предусматривают похожие формы подмены, похожие на те, которые используются при фишинге сайтов, когда визуально символы похожи друг на друга и их подмена на первый взгляд не видна. Например, KERNE132.dll – на самом деле будет подделкой, тогда как в правильном процессе вместо 1 (единицы) должна стоять буква L – KERNEL32.dll. Правильное местонахождение этого файла – в папке Windows\System32, но некоторые Malware кладут его в другое место – в папку Windows\System.
Можно удостовериться, не зависла ли в памяти уже закрытая программа, в том месте, где ее уже давно быть не должно.
Еще может быть вариант, когда программа в памяти держит несколько копий себя, хотя никакого сервиса на текущий момент с таким названием пользователь не запускал.
Закройте все приложения, и если после этого, проверяя объем занятой памяти, вы видите, что какой-то сервис занял почти все ресурсы, его стоит проверить, и особенно это подозрительно, если активность памяти такого ресурса никак нельзя просчитать.
How do I get spyware?
Spyware can infect your system in the same ways as any other form of malware. Here are a few of spyware’s main techniques to infect your PC or mobile device.
- Security vulnerabilities, e.g. backdoors and exploits. An exploit is a security vulnerability in your device’s hardware or software that can be abused or exploited to gain unauthorized access. Software vulnerabilities are also known as “software bugs” or just “bugs” for short. Exploits are an unintentional byproduct of hardware and software manufacturing. Mistakes happen and bugs manage to find their way in to even the most polished consumer technology. Backdoors, on the other hand, are put in place on purpose as a way to quickly gain access to your system after the fact. Sometimes the hardware and software makers themselves put the backdoors in. More often than not, however, cybercriminals will use an exploit to gain initial access to your system then install a permanent backdoor for future access.
- Phishing and spoofing. These two threats are often used in tandem. Phishing happens whenever criminals try to get you to perform some sort of action such as clicking a link to a malware-laden website, opening an infected email attachment (aka malspam), or giving up your login credentials. Spoofing refers to the act of disguising phishing emails and websites so that they appear to be from and by individuals and organizations you trust.
- Misleading marketing. Spyware authors love to present their spyware programs as useful tools to download. It might be an Internet accelerator, new download manager, hard disk drive cleaner, or an alternative web search service. Beware this kind of “bait,” because installing it can result in inadvertent spyware infection. And even if you eventually uninstall the “useful” tool that initially introduced the infection, the spyware remains behind and continues to function.
- Software bundles. Who doesn’t love free software (freeware)? Except when it’s a host program that conceals a malicious add-on, extension, or plugin. Bundleware may look like necessary components, but they are nonetheless spyware, which, again, remains even if you uninstall the host application. Making matters worse, you may find that you actually agreed to install the spyware when you accepted the terms of service for the original application.
- Trojans. Broadly speaking, if malware pretends to be something it’s not—that means it’s a Trojan. That said, most Trojans today are not threats in and of themselves. Rather, cybercriminals use Trojans to deliver other forms of malware, like cryptojackers, ransomware, and viruses.
- Mobile device spyware. Mobile spyware has been around since mobile devices became mainstream. Mobile spyware is especially devious since mobile devices are small and users generally can’t see what programs are running in the background as easily as they might on their laptop or desktop. Both Mac and Android devices are vulnerable to spyware. These apps include legitimate apps recompiled with harmful code, straight up malicious apps posing as legitimate ones (often with names resembling popular apps), and apps with fake download links.
“Mobile spyware has been around since mobile devices became mainstream.”
How does malware affect my business?
Malware attacks on businesses went up 55 percent in the second half of 2018 with banking Trojans and ransomware proving to be the most popular types of attacks. Specifically, Trojan attacks on businesses rose 84 percent while ransomware attacks went up 88 percent.
So why are cybercriminals bullish on business attacks? The answer is simple: businesses present a broader attack surface and more bang for the buck. In one noteworthy example, the Emotet banking Trojan hobbled critical systems in the City of Allentown, PA, requiring help from Microsoft’s incident response team to clean up and racking up remediation costs to the tune of $1 million.
In another example, the SamSam ransomware brought the City of Atlanta to its knees by taking down several essential city services—including revenue collection. Ultimately, the SamSam attack cost Atlanta $2.6 million to remediate.
While Emotet and SamSam grab the headlines, the majority of ransomware cases as of late have been the result of GandCrab. First detected in January of 2018, the GandCrab ransomware has already gone through several iterations as its authors try to avoid detection and strengthen encryption. It’s been estimated GandCrab has already netted its authors somewhere around $300 million in paid ransoms, with individual ransoms set from $600 to $700,000.
Considering the tremendous cost associated with a malware attack, and the current rise of ransomware and banking Trojans in particular, here’s some tips on how to protect your business from malware.
- Implement network segmentation. Spreading your data onto smaller subnetworks reduces your attack surface—smaller targets are harder to hit. This can help contain a breach to only a few endpoints instead of your entire infrastructure.
- Enforce the principle of least privilege (PoLP). In short, give users the access level they need to do their jobs and nothing more. Again, this helps to contain damages from breaches or ransomware attacks.
- Backup all your data. This goes for all the endpoints on your network and network shares too. As long as your data is archived, you can always wipe an infected system and restore from a backup.
- Educate end users on how to spot malspam. Users should be wary of unsolicited emails and attachments from unknown senders. When handling attachments, your users should avoid executing executable files and avoid enabling macros on Office files. When in doubt, reach out. Train end users to inquire further if suspicious emails appear to be from a trusted source. One quick phone call or email goes a long way towards avoiding malware.
- Educate staff on creating strong passwords and implement some form of multi-factor authentication (MFA)—two-factor authentication at a bare minimum.
- Patch and update your software. Microsoft releases security updates the second Tuesday of every month and many other software makers have followed suit. Stay in the loop on important security updates by subscribing to the Microsoft Security Response Center blog. Expedite the patch process by launching updates at each endpoint from one central agent, as opposed to leaving it up to each end user to complete on their own time.
- Get rid of end of abandonware. Sometimes it’s hard to get rid of old software that’s past its expiration date—especially at a large business where the purchasing cycle moves with the urgency of a sloth, but discontinued software is truly the worst-case scenario for any network or system administrator. Cybercriminals actively seek out systems running outdated and obsolete software so replace it as soon as possible.
- Get proactive about endpoint protection. Malwarebytes, for example, has multiple options for your business with Endpoint Protection and Endpoint Detection and Response.
What’s the difference between antivirus and anti-malware?
For the most part, “antivirus” and “anti-malware” mean the same thing. They both refer to software designed to detect, protect against, and remove malicious software. Contrary to what the name might suggest, antivirus software protects against more than viruses–it just uses a slightly antiquated name to describe what it does. Anti-malware software is designed to protect against viruses too. Anti-malware just uses a more modern name that encompasses all kinds of malicious software, including viruses. That being said, anti-malware can stop a viral infection form happening and remove infected files. However, anti-malware isn’t necessarily equipped to restore files that have been changed or replaced by a virus. Both antivirus and anti-malware fall under the broader term “cybersecurity.”
The future of cybersecurity programs (which is already here)
Artificial intelligence (AI) and machine learning (ML) are the latest stars in anti-malware technology.
AI allows machines to perform tasks for which they are not specifically pre-programmed. AI does not blindly execute a limited set of commands. Rather, AI uses “intelligence” to analyze a situation, and take action for a given goal such as identifying signs of ransomware activity.
ML is programming that’s capable of recognizing patterns in new data, then classifying the data in ways that teach the machine how to learn.
Put another way, AI focuses on building smart machines, while ML uses algorithms that allow the machines to learn from experience. Both these technologies are a perfect fit for cybersecurity, especially since the number and variety of threats coming in every day are too overwhelming for signature-based methods or other manual measures. Both AI and ML are still in developmental phases, but they hold immense promise.
In fact, at Malwarebytes, we already use a machine-learning component that detects malware that’s never been seen before in the wild, also known as zero-days or zero-hours. Other components of our software perform behavior-based, heuristic detections—meaning they may not recognize a particular code as malicious, but they have determined that a file or website is acting in a way that it shouldn’t. This tech is based on AI/ML and is available to our users both with real-time protection and on-demand scanning.
In the case of business IT professionals with multiple endpoints to secure, the heuristic approach is especially important. We never know what the next big malware threat will be. So heuristics plays an important role in Malwarebytes Endpoint Protection, as does AI and ML. Together, they create multiple layers of protection that address all stages of the attack chain for both known and unknown threats.
Do Macs get malware?
Conventional wisdom has sometimes held that Macs and iPads are immune to catching viruses (and don’t need an antivirus). For the most part, that’s true. At the very least, it hasn’t happened
in a long time.
“Mac systems are subject to the same vulnerabilities (and subsequent symptoms of infection) as Windows
machines and cannot be considered bulletproof.”
Other kinds of malware are a different story. Mac systems are subject to the same vulnerabilities (and subsequent
symptoms of infection) as Windows machines and cannot be considered bulletproof. For instance, the Mac’s
built-in protection against malware doesn’t block all the adware and spyware bundled with fraudulent
application downloads. Trojans and keyloggers are also threats. The first detection of ransomware written
specifically for the Mac occurred in March 2016, when a Trojan-delivered attack affected more than 7,000 Mac users.
In fact, Malwarebytes saw more Mac malware in 2017 than in any previous year. By the end of 2017, the number of new
unique threats that our professionals counted on the Mac platform was more than 270 percent higher compared to the
number noted in 2016.
For more on the state of Mac malware, visit the Malwarebytes blog site here.
What is malware?
Malware, or “malicious
software,” is an umbrella term that describes any malicious program or code that is harmful to systems.
Hostile, intrusive, and intentionally nasty, malware seeks to invade, damage, or disable computers, computer
systems, networks, tablets, and mobile devices, often by taking partial control over a device’s operations.
Like the human flu, it interferes with normal functioning.
Malware is all about making money off you illicitly. Although malware cannot damage the physical hardware of systems
or network equipment (with one known exception—see the Google Android section below), it can steal, encrypt, or
delete your data, alter or hijack core computer functions, and spy on your computer activity without your knowledge
or permission.
How Malwarebytes Premium protects you
At Malwarebytes, we are serious about infection prevention, which is why we aggressively block both websites and advertisements that we consider fraudulent or suspicious. For example, we block torrent sites like The Pirate Bay. Though many savvy users have used such sites without issue, some of the files they offer for download are really Trojans. For similar reasons, we also block cryptomining through browsers, but the user can choose to turn off the block and connect.
Our reasoning is that it’s better to err on the side of safety. If you want to take the risk, it’s easy to whitelist a site, but even tech-savvy types can fall for a convincing Trojan.
To learn more about Trojans, malware, and other cyberthreats, check out the Malwarebytes Labs blog. The things you learn may just help you avoid an infection down the road.
How can I tell if my iPhone or iPad has malware?
If your smartphone’s name begins with a lower-case “i,” then pat yourself on the back, because
malware is not a significant issue on the iPhone. That is not to say it doesn’t exist, but it’s extremely rare. In
fact, suffering a malware infection on an iPhone mostly only happens in two extraordinary circumstances.
“While outright malware infections are unlikely, using an iPhone doesn’t protect you at all against
scam phone calls or scam text messages.”
The first consists of a targeted attack by a nation-state-level adversary—a government that has either created or
purchased at a cost of millions of dollars a piece of malware engineered to take advantage of some obscure security
hole in the iOS. Don’t be shocked, because all devices have some sort of vulnerability. To be sure, Apple has
done a fine job of securing iOS, even preventing any apps (including security software) from scanning the phone or
other apps on the device’s system. That’s why it’s so expensive to engineer malware that installs
its code for whatever kind of remotely executed activity the offending nation-state needs.
One particularly
noteworthy instance happened in 2016 when an internationally recognized human rights defender, based in the
United Arab Emirates (UAE), received SMS text messages on his iPhone promising “new secrets” about
detainees tortured in UAE jails. The targeted recipient was invited to click on an included link. He didn’t,
but instead sent the message to cybersecurity researchers, who identified it as containing an exploit that would have
turned the activist’s phone into a digital spy.
The second instance is when a user makes an iPhone vulnerable by means of jailbreaking, which removes the
restrictions and limitations Apple imposes, chiefly to ensure that software apps can only be installed from the App
Store. Apple carefully vets the app developers it carries, even though malware piggybacking on a legitimate app has
happened.
One more point. While outright malware infections are unlikely, using an iPhone doesn’t protect you at all
against scam phone calls or scam text messages. If you tap a link in a message from an unknown source (or someone you
know who’s being impersonated, or “spoofed”), it could send you to a site that asks for your login
and other personal information. So there are still plenty of ways that you can become a victim. Always proceed with
caution.
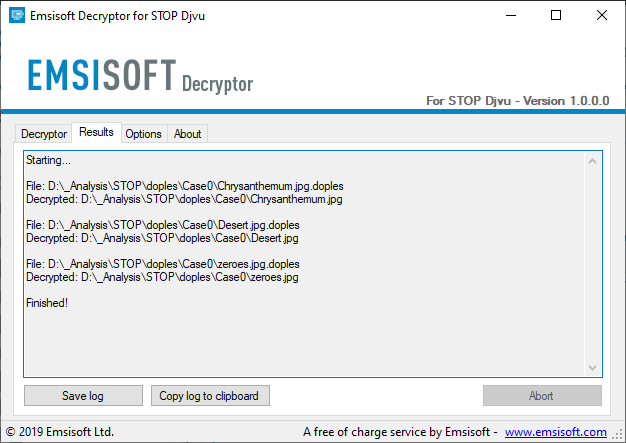
How can I remove Emotet?
If you suspect you’ve already been infected by Emotet, don’t freak out. If your computer is connected to a network—isolate it immediately. Once isolated, proceed to patch and clean the infected system. But you’re not done yet. Because of the way Emotet spreads across your network, a clean computer can be re-infected when plugged back into an infected network. Clean each computer on your network one-by-one. It’s a tedious process, but Malwarebytes business solutions can make it easier, isolating and remediating infected endpoints and offering proactive protection against future Emotet infections.
If knowing is half the battle, head on over to the Malwarebytes Labs and you can learn more on how Emotet evades detection and how Emotet’s code works.
Unlike some other types of malware, spyware authors do not really target specific groups or people. Instead, most spyware attacks cast a wide net to collect as many potential victims as possible. And that makes everyone a spyware target, as even the slightest bit of information might find a buyer.
“Spyware attacks cast a wide net to collect as many potential victims as possible.”
Information obtained through stolen documents, pictures, video, or other digital items can even be used for extortion purposes.
So, at the end of the day, no one is immune from spyware attacks, and attackers usually care little about whom they are infecting, as opposed to what they are after.